passwdqc for Windows - password/passphrase policy enforcement
passwdqc is a well-known proactive password and
passphrase strength checking and policy enforcement toolset.
It is available for (and included as part of)
a variety of Unix-like systems since 2000 (with many updates),
and is now also offered for Windows.
Supported are both domain controllers and end-user systems.
Full support for passphrases,
extensive testing
[1]
[2]
[3]
on real-world passwords,
being able to exactly match the policy you use on Unix (if applicable),
bundled end-user programs (their use is optional),
and simple site-wide licensing and pricing
(not per-user, nor per-computer)
differentiate this product from the competition.
The product, once installed, registers with the system a
password filter DLL, which is where the policy is enforced.
There are three GUI programs: Configuration, Change Password,
and Reset Password -
please see the screenshots.
The latter two programs may be used to easily duplicate the domain controller's
password policy on end-user systems, so that the users are informed of the
specific reason why their initial choice of new password did not meet policy
and are offered randomly-generated passphrases.
Finally, also included are three command-line programs: pwqcheck, pwqfilter, and pwqgen.
These are non-essential for use of the Windows product, but might be handy for those readily familiar with passwdqc on Unix.
In terms of backwards compatibility, we currently support Server 2008 or Vista and above,
but of course we recommend that you actually use newer Windows versions currently supported by Microsoft.
Download:
The free downloads offered above are for pre-purchase evaluation only (no more than 30 days of consecutive use),
unless and until you purchase a license.
Purchase:
The links above allow you to pay online with a variety of payment methods, or to choose to pay offline.
Your purchase will be from FastSpring, a trusted reseller of software products and services.
Your private download directory will be created and a link to it e-mailed to you immediately upon receipt of your payment.
Your purchase is primarily of licenses (legal right) to use the software and of access to the binary filters.
At a later time, your private download directory will also be the place to download any upgrades you're entitled to.
Unconditional 7-day money back guarantee
for purely online payments (including credit card payments, but not including bank wire transfers):
if you're for any reason or for no reason at all unsatisfied with the products or services,
we will refund your payment on your request if the request arrives within 7 days after your payment date.
Low price guarantee:
our prices on this product are the lowest you can find.
If you find a better price on a commercial product with at least the same functionality, for the same operating system,
with upgrades and support similar to those included with your purchase, and if you inform us within 30 days of your payment,
we will gladly refund the price difference.
Shop with confidence!
Please don't hesitate to e-mail us at <orders at openwall.com>
if you experience any problems placing an order or completing your download, or to request a refund.
There are currently two recommended common password filter files included with a passwdqc license purchase:
one preventing reuse of passwords that appeared 100+ times in leaks or breaches that the
HIBP (Pwned Passwords) database version 7 builds upon
or 10+ times in the RockYou leak (the de-facto gold standard for password cracking),
and another with these thresholds at 20+ for HIBP and 3+ for RockYou.
These two files encode, respectively, 2+ million passwords in 9 MiB file size and 14+ million passwords in 58 MiB.
Also included is a similar filter additionally encoding all of RockYou (no threshold),
for a total of 25+ million passwords in 100 MiB,
and mostly for research purposes a filter encoding only all of RockYou's (different) 14+ million passwords in 56 MiB (no HIBP).
The subscription to leaked password filter files provides regularly updated files preventing reuse of
all passwords from the latest version of HIBP (also includes RockYou).
Due to our extremely efficient encoding, the current 847+ million unique leaked or breached passwords (from billions of accounts)
are represented in a 3.3 GiB (3.5 GB) file.
This is many times smaller than a download of the original HIBP files, yet allows for instant lookup.
Our setup and tools are ready for further growth of the unique password count, if necessary well into the billions.
This kind of checking of user-provided passwords against existing data breaches is recommended in the current
NIST guidance, specifically in
publication 800-63B sections 5.1.1.2 and
A.3.
For the curious, under the hood passwdqc binary filters are improved
cuckoo filters, a modern probabilistic data structure.
They never produce false negatives (that is, all passwords that are meant to be denied will always be).
They occasionally produce false positives (that is, a previously unseen password might be unintentionally denied),
but with our settings and algorithm this probability is negligible (on average 1 occurrence per 1.15 billion attempted passwords).
Looking up a password against a filter requires at most two tiny random disk reads,
which is very quick and lightweight for the server.
passwdqc for Windows - screenshots made on Windows 8.1
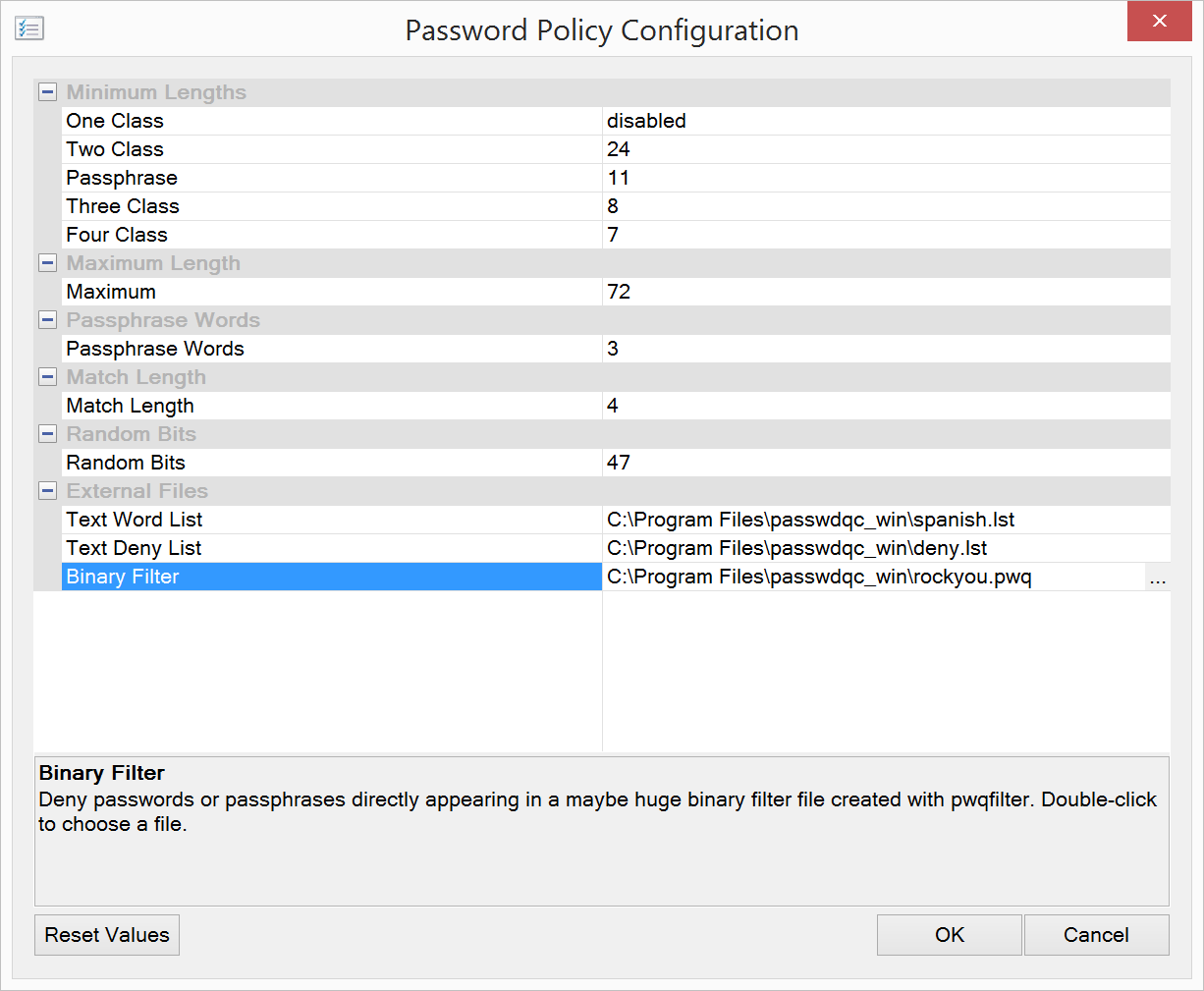
Configuration utility:
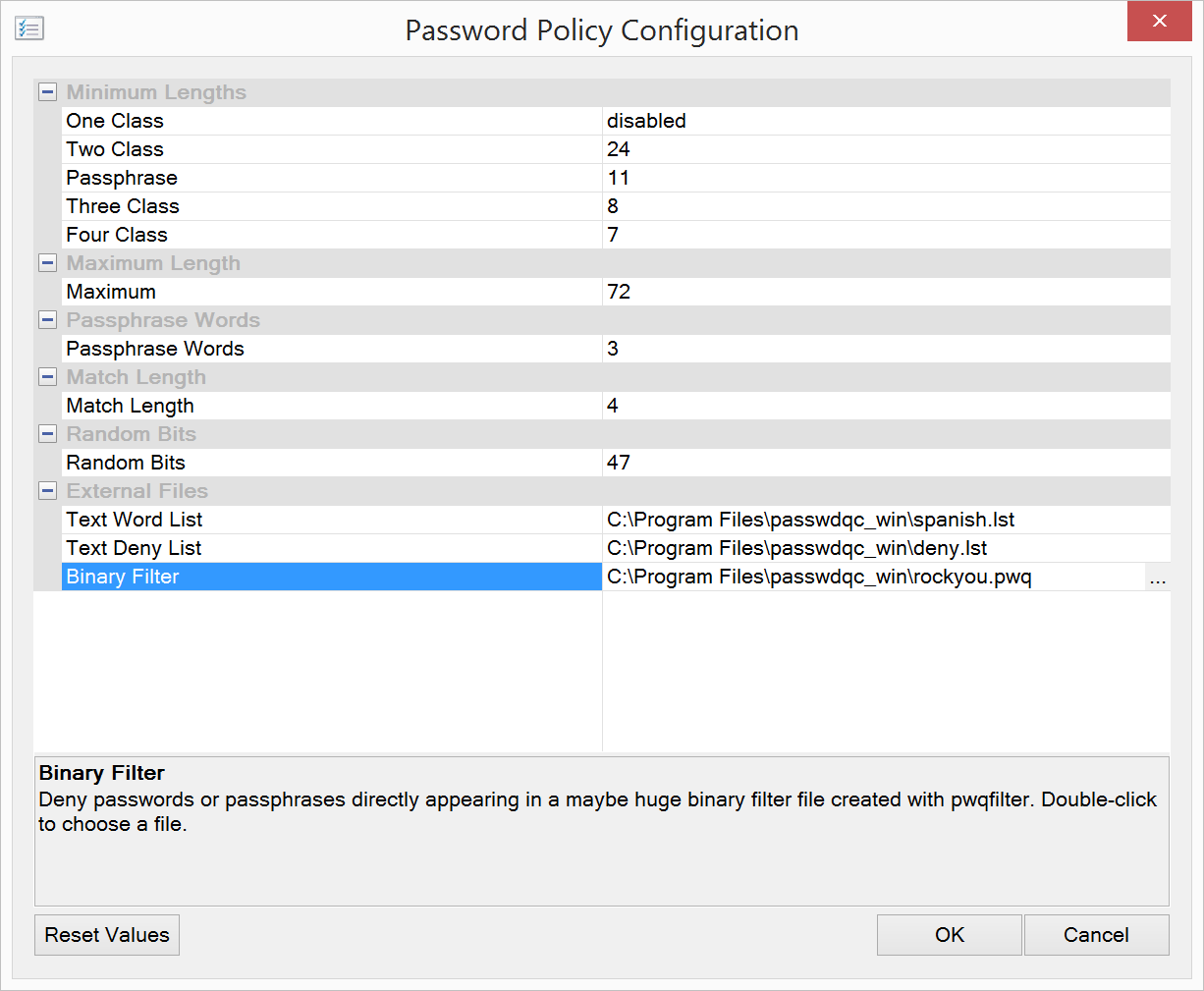
|
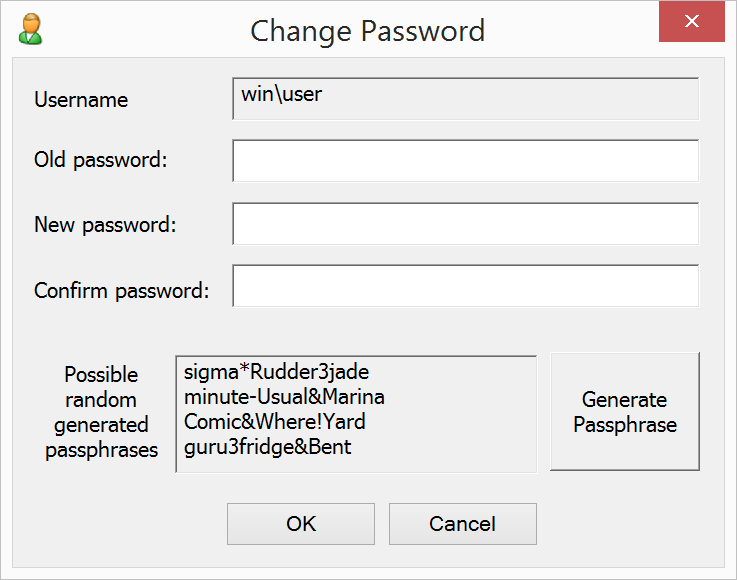
Change Password utility:
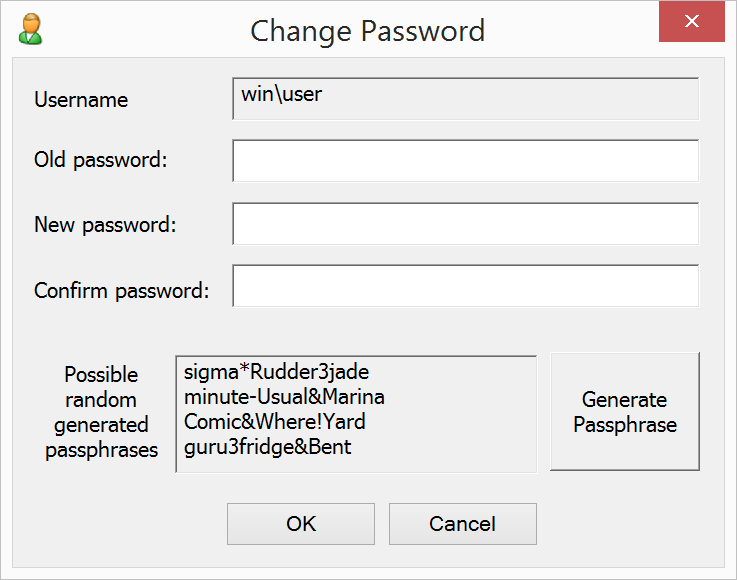
The generated passphrases have been confirmed to meet the expected statistical properties
(no excessive repetitions among millions generated for testing purposes on Windows 8.1 64-bit).
We use
CryptGenRandom, an
interface to Windows' cryptographically secure pseudorandom number generator.
|
|
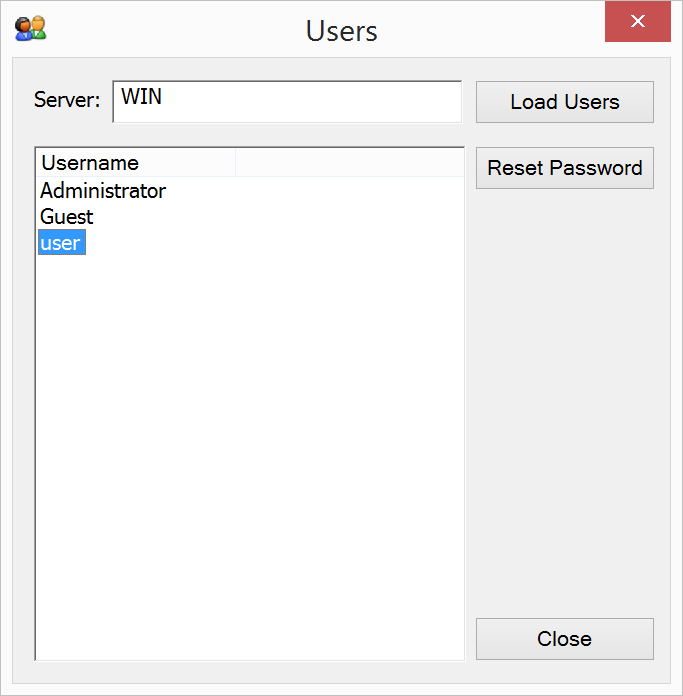
Reset Password utility, user choice dialog:
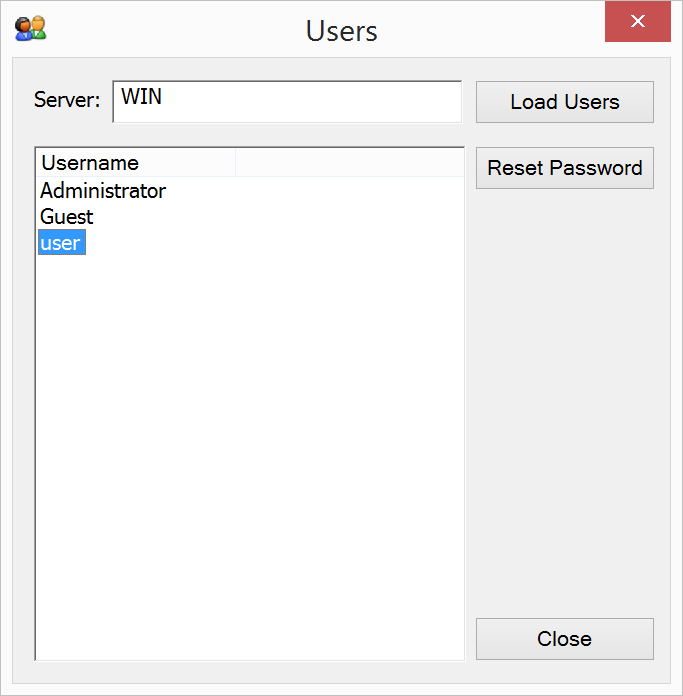
|
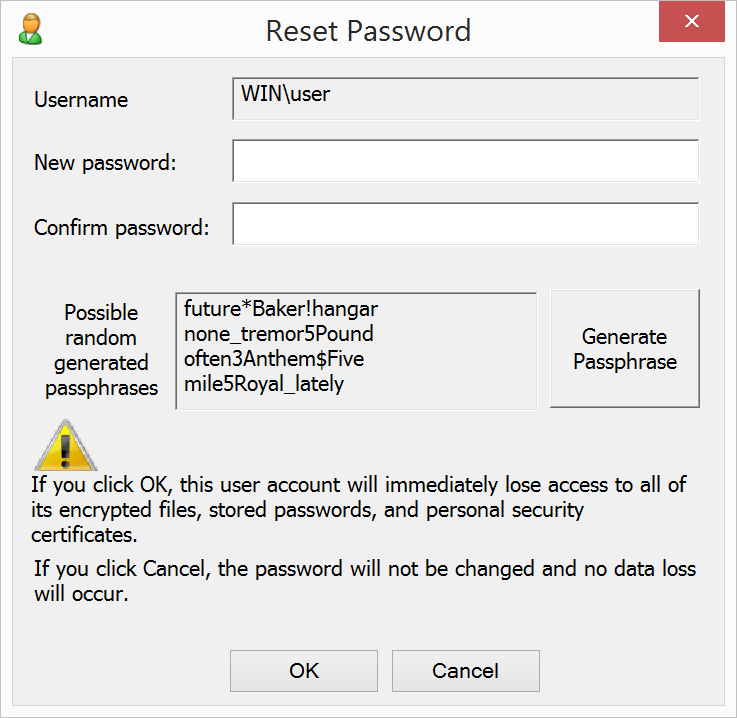
Reset Password utility, new password dialog:
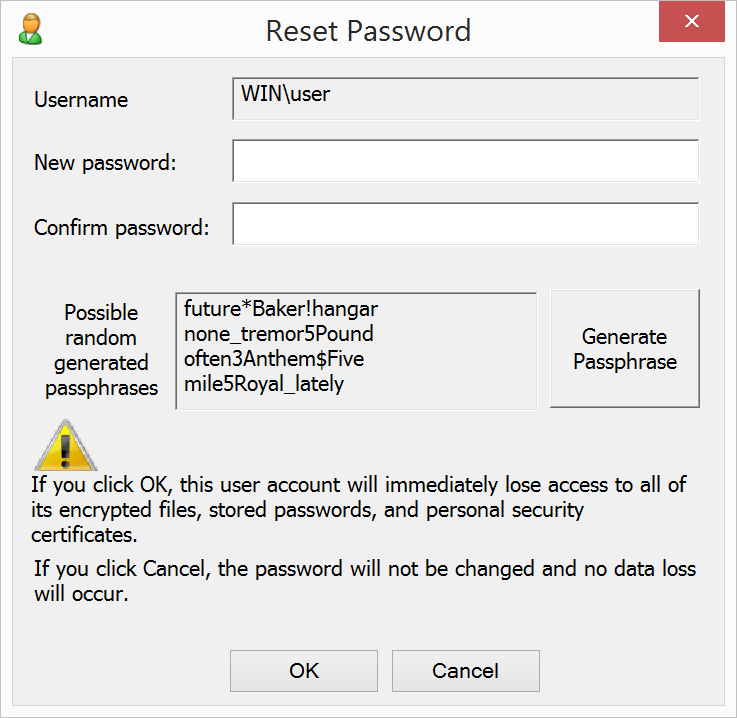
|
224081